Hashicorp Vault - Setup

Installation
Before I was using the package managers to install nomad and consul - and ran into a few issues with it. So now I want to follow the manual installation guide (see manual binary download) instead.
Download
wget https://releases.hashicorp.com/vault/1.8.2/vault_1.8.2_linux_amd64.zip
unzip vault_1.8.2_linux_amd64.zip
sudo mv vault /usr/bin
rm vault_1.8.2_linux_amd64.zip
And verify that it was installed successfully:
vault -v
Vault v1.8.2 (aca76f63357041a43b49f3e8c11d67358496959f)
We can also add the autocomplete function:
vault -autocomplete-install
complete -C /usr/bin/vault vault
Configure Vault
Create the configuration directory:
sudo mkdir /etc/vault.d
And create the basic configuration file:
sudo nano /etc/vault.d/config.hcl
storage "consul" {
address = "192.168.2.110:8500"
path = "vault/"
}
listener "tcp" {
address = "192.168.2.110:8200"
tls_disable = 1
}
api_addr = "http://192.168.2.110:8200"
cluster_addr = "https://192.168.2.110:8201"
ui = true
As Storage I have chosen the Consul k/v store with a prefix of vault/. Alternatively, you can also store the Vault data to file:
storage "file" {
path = "/opt/vault/data"
}
Firewall
I used the port 80 here for the Vault service - make sure that your firewall allows traffic in on the port you choose there:
firewall-cmd --permanent --zone=public --add-port=8200/tcp
firewall-cmd --permanent --zone=public --add-port=8201/tcp
firewall-cmd --reload
firewall-cmd --zone=public --list-ports
Prepare System.d Service
sudo nano /etc/systemd/system/vault.service
Create the service file:
[Unit]
Description="HashiCorp Vault - A tool for managing secrets"
Documentation=https://www.vaultproject.io/docs/
Requires=network-online.target
After=network-online.target
ConditionFileNotEmpty=/etc/vault.d/config.hcl
StartLimitIntervalSec=60
StartLimitBurst=3
[Service]
ProtectSystem=full
ProtectHome=read-only
PrivateTmp=yes
PrivateDevices=yes
SecureBits=keep-caps
AmbientCapabilities=CAP_IPC_LOCK
Capabilities=CAP_IPC_LOCK+ep
CapabilityBoundingSet=CAP_SYSLOG CAP_IPC_LOCK
NoNewPrivileges=yes
ExecStart=/usr/bin/vault server -config=/etc/vault.d/config.hcl
ExecReload=/bin/kill --signal HUP $MAINPID
KillMode=process
KillSignal=SIGINT
Restart=on-failure
RestartSec=5
TimeoutStopSec=30
StartLimitInterval=60
StartLimitIntervalSec=60
StartLimitBurst=3
LimitNOFILE=65536
LimitMEMLOCK=infinity
LogRateLimitIntervalSec=0
LogRateLimitBurst=0
[Install]
WantedBy=multi-user.target
Reload SystemD:
sudo systemctl daemon-reload
service vault status
And add the following exports to your shell config (e.g. ~/bashrc, ./zshrc):
echo "export VAULT_ADDR=http://192.168.2.110:8200" >> ~/.zshrc
source ~/.zshrc
Now we can start the service:
sudo service vault start
sudo service vault status
sudo systemctl enable vault
Initialize Vault
vault operator init
Unseal Key 1: vanBssslvadjyp9jptzsAPO4uWGK1ZsT8FYW/qpS36iJ
Unseal Key 2: g6OsArgXl0+K0AUaSZJb8eNXAX1nfdKMdrRJfu8zIug1
Unseal Key 3: MHj+gJhnIgXI6mKxt3lHmtvJEgypaEczGeZF5Ep4uKgX
Unseal Key 4: i8HXZ90nHzo3aku+S37JDzeXGUxZX+H5WE4632gO2cjY
Unseal Key 5: 4ixQc9p7whDWkSr8lW8r5b1w0LodNGOxGIZP5kFdwZ29
Initial Root Token: s.TFCSNUDRJbuBGjOkgaqSfEQR
Vault initialized with 5 key shares and a key threshold of 3. Please securely
distribute the key shares printed above. When the Vault is re-sealed,
restarted, or stopped, you must supply at least 3 of these keys to unseal it
before it can start servicing requests.
Vault does not store the generated master key. Without at least 3 keys to
reconstruct the master key, Vault will remain permanently sealed!
It is possible to generate new unseal keys, provided you have a quorum of
existing unseal keys shares. See "vault operator rekey" for more information.
RECOVERY: All the information are stored in the Consul k/v store under the path you defined inside your Vault config
consul kv get -recurse. To reset all of this first delete all Vault keys from the Consul k/v storeconsul kv delete -recurse vault/, restart Vaultsudo service vault restartand reinitializevault operator init
To unseal Vault we now can use three of the Unseal Keys:
vault operator unseal vanBssslvadjyp9jptzsAPO4uWGK1ZsT8FYW/qpS36iJ
Key Value
---
-----
Seal Type shamir
Initialized true
Sealed true
Total Shares 5
Threshold 3
Unseal Progress 1/3
Unseal Nonce 10ab3b57-8dba-f89b-0ad5-d941d1a8e8dd
Version 1.8.2
Storage Type consul
HA Enabled true
vault operator unseal g6OsArgXl0+K0AUaSZJb8eNXAX1nfdKMdrRJfu8zIug1
Key Value
---
-----
Seal Type shamir
Initialized true
Sealed true
Total Shares 5
Threshold 3
Unseal Progress 2/3
Unseal Nonce 10ab3b57-8dba-f89b-0ad5-d941d1a8e8dd
Version 1.8.2
Storage Type consul
HA Enabled true
vault operator unseal MHj+gJhnIgXI6mKxt3lHmtvJEgypaEczGeZF5Ep4uKgX
Key Value
---
-----
Seal Type shamir
Initialized true
Sealed false
Total Shares 5
Threshold 3
Version 1.8.2
Storage Type consul
Cluster Name vault-cluster-825513f4
Cluster ID 95834c86-b5a6-e3fa-a5d3-a05c977dac8a
HA Enabled true
HA Cluster n/a
HA Mode standby
Active Node Address <none>
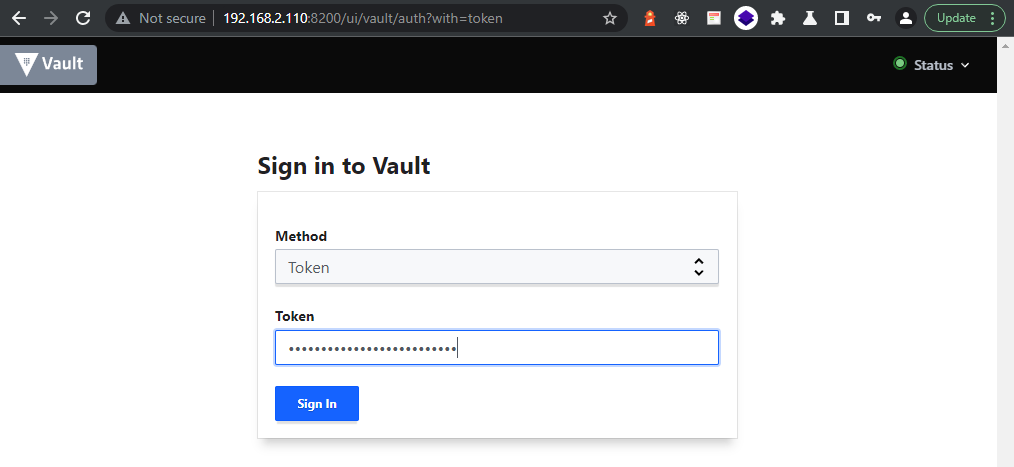
Accessing the UI
I have configured Vault to start the user interface on http://192.168.2.110:8200 - there you can use the root token to unlock the UI:
Initial Root Token: s.TFCSNUDRJbuBGjOkgaqSfEQR
This token is the Root Token and should not be used by default - I am just going to use it for the set up process and later create a set of different tokens for different tasks. But for now:
echo "export VAULT_TOKEN=s.TFCSNUDRJbuBGjOkgaqSfEQR" >> ~/.zshrc
source ~/.zshrc
This way I am now able to use both the UI and the CLI to interact with the Vault API:
vault secrets list
Path Type Accessor Description
---- ---- -------- -----------
cubbyhole/ cubbyhole cubbyhole_afe308c4 per-token private secret storage
identity/ identity identity_76793f2d identity store
sys/ system system_88682e7c system endpoints used for control, policy and debugging